Deepfakes

Yassine Yousfi
Yassine Yousfi
| BC (Before ChatGPT) | AD (After Deep Learning) |
|---|---|
| Digital Images | Social Media |
| Text Messages and Emails | Large Language Models generated content |
| Static Documents | AI Agents Automation |

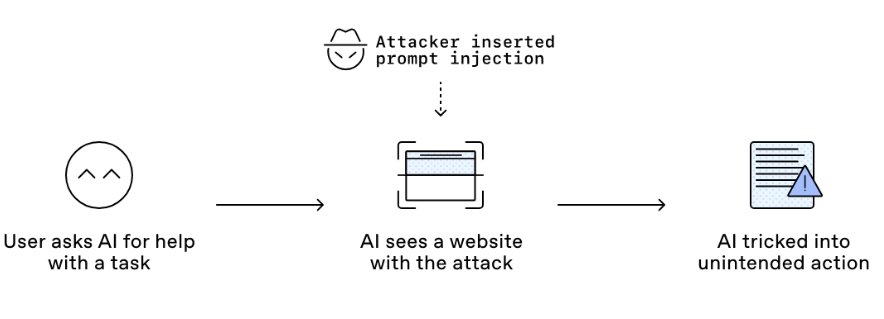
Source: Understanding prompt injections: a frontier security challenge. OpenAI
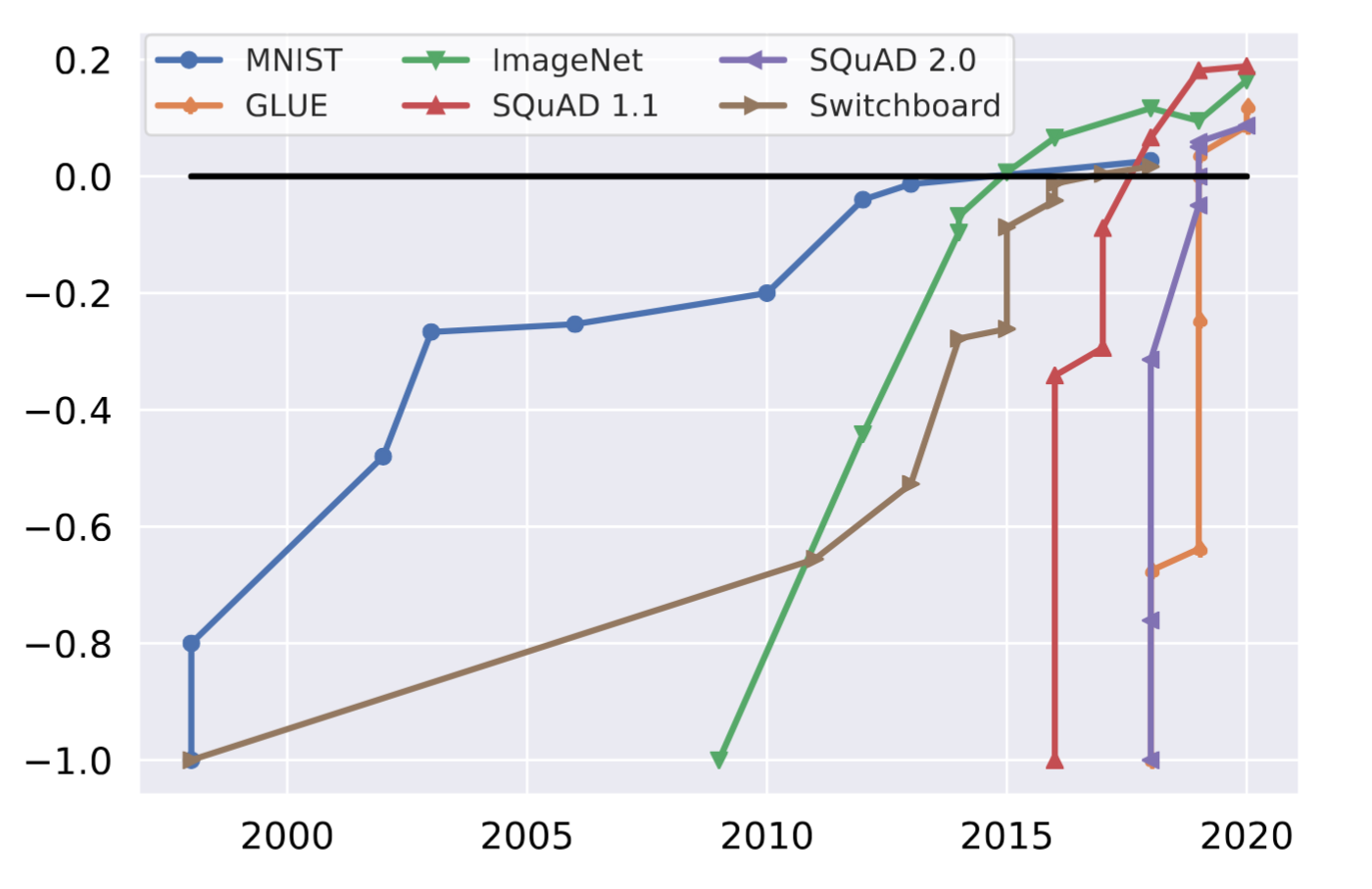
Kiela, Douwe, et al. "Dynabench: Rethinking benchmarking in NLP."
Proceedings of the 2021 conference of the North American chapter of the Association for Computational Linguistics
Original
Significant Bit
Bit Plane
Cover
Bit Plane
Character
Stego
Stego Bit Plane
Cover
Kernel
Convolved

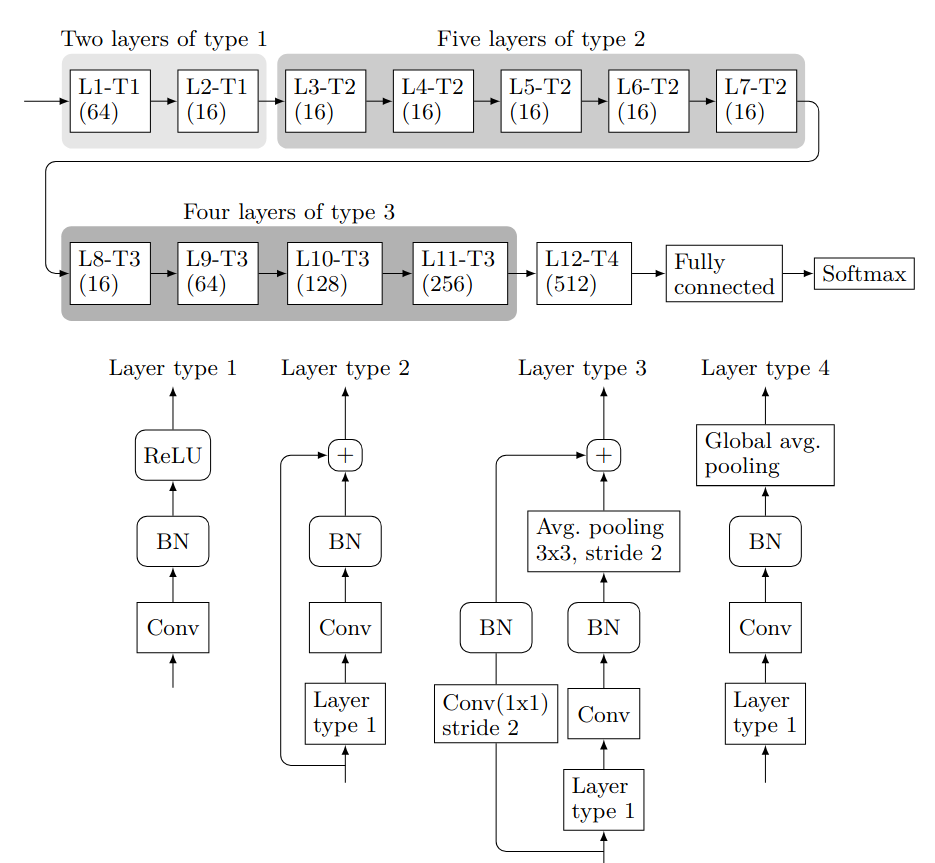
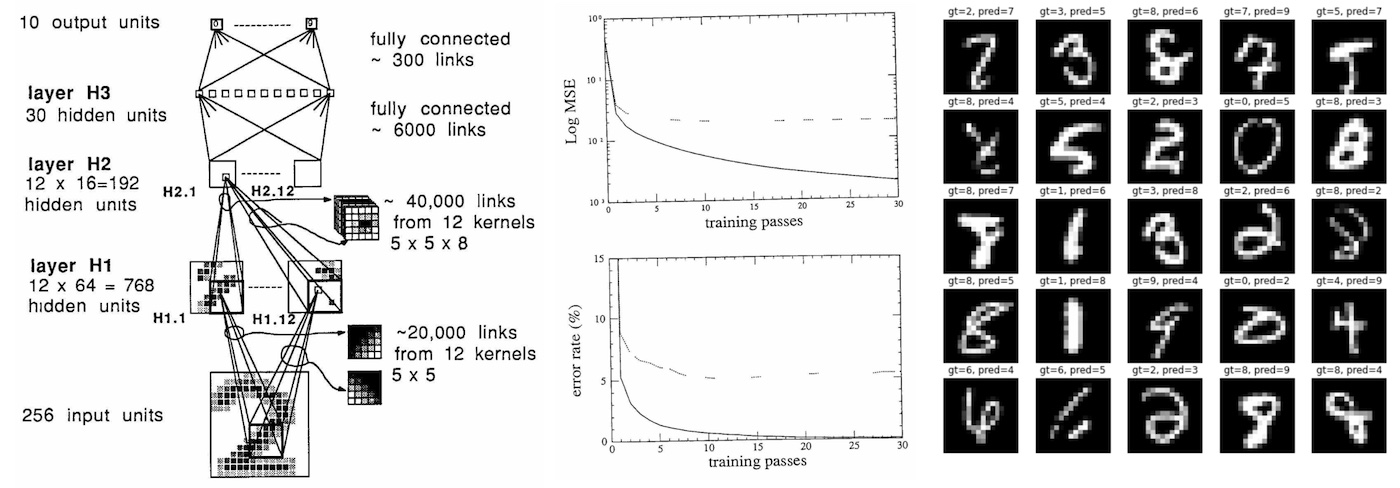
Boroumand, Mehdi, Mo Chen, and Jessica Fridrich. "Deep residual network for steganalysis of digital images." IEEE Transactions on Information Forensics and Security 14.5 (2018)
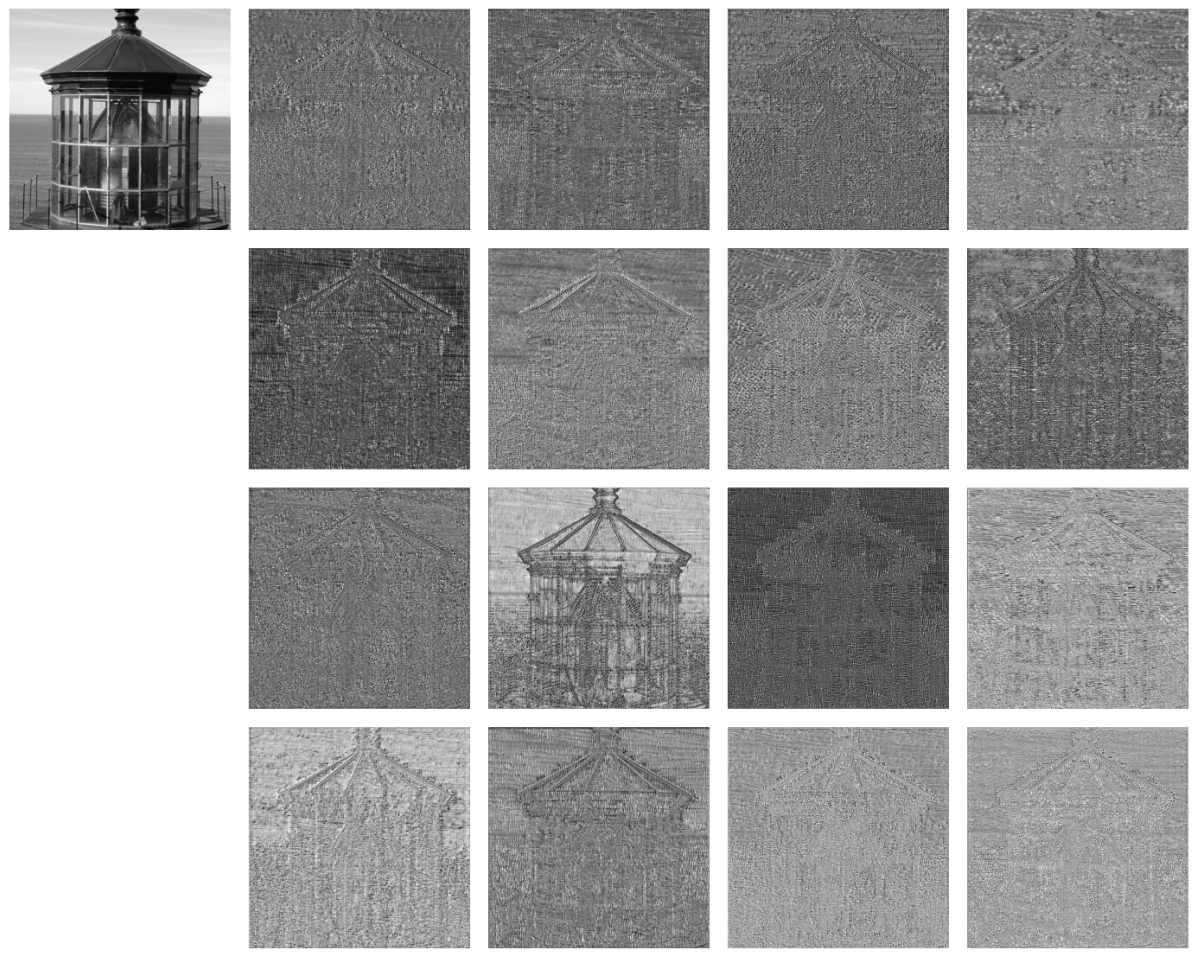
Outputs of Layer 7 from SRNet visualized as grayscale images.
Yousfi, Yassine. "Deep Learning for Image Steganography and Steganalysis: Challenges, Advances, and Opportunities." State University of New York at Binghamton, 2022.
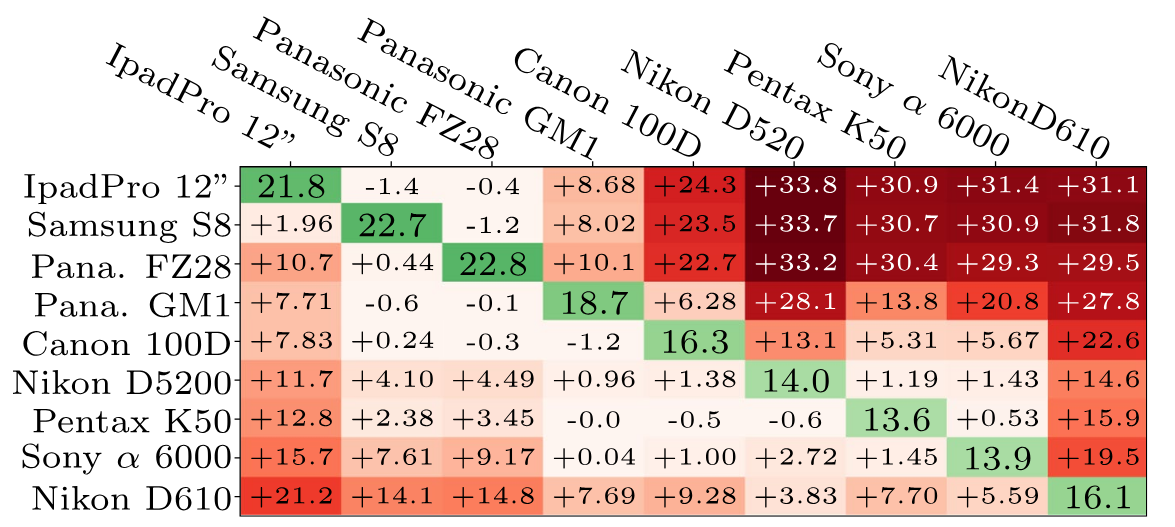
Giboulot, Quentin, et al. "Effects and solutions of cover-source mismatch in image steganalysis." Signal Processing: Image Communication 86 (2020)

Examples of visible local traces of Steganography found using SRNet.
Yousfi, Yassine, Jan Butora, and Jessica Fridrich. "CNN steganalyzers leverage local embedding artifacts." 2021 IEEE International Workshop on Information Forensics and Security (WIFS). IEEE, 2021.
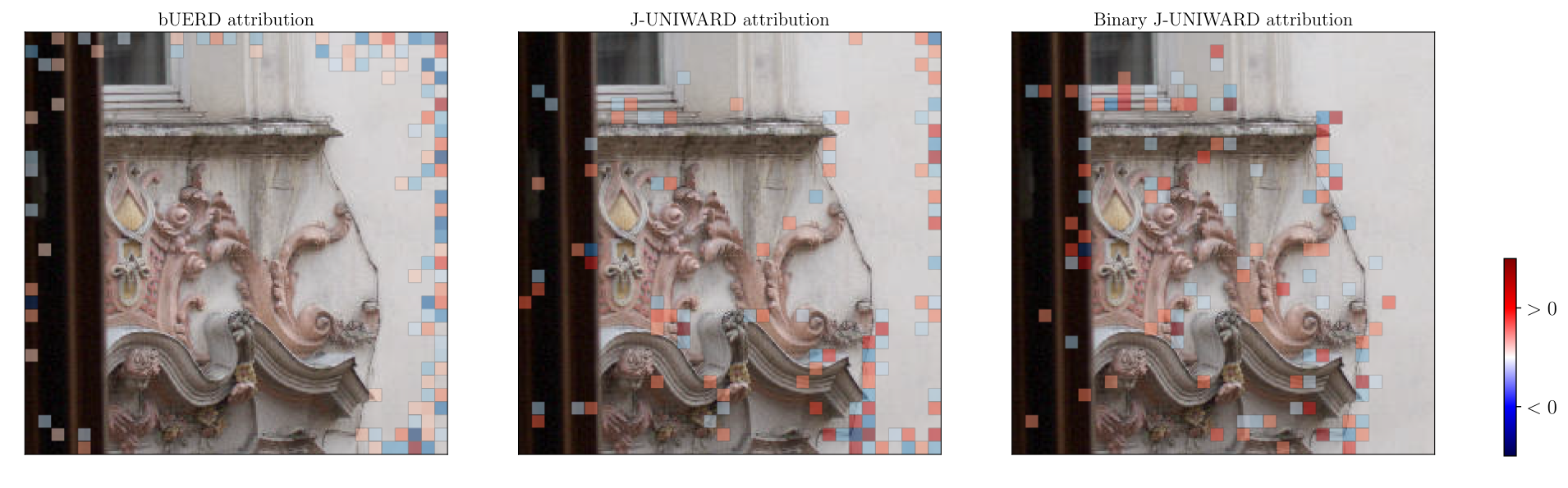
Examples of visible local traces of Steganography found using SRNet.
Yousfi, Yassine, Jan Butora, and Jessica Fridrich. "CNN steganalyzers leverage local embedding artifacts." 2021 IEEE International Workshop on Information Forensics and Security (WIFS). IEEE, 2021.
AUTO STEGO

Source: Shutterstock lol
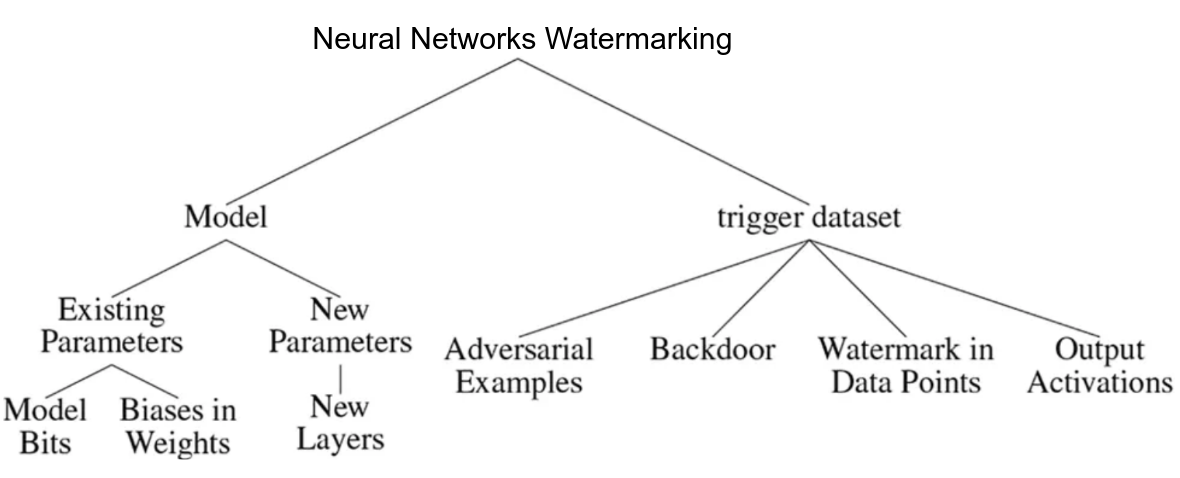
Boenisch, Franziska. "A systematic review on model watermarking for neural networks." Frontiers in Big Data 4 (2021).